With over 80 NERC standards to follow, it is difficult for wind farm owners, operators, and employees to meet the organization’s requirements and make sure all parties involved are up-to-date on training. But clearly documented procedures and training ensures that operating personnel understand and can comply with requirements.
 Users, owners, and operators of the bulk electric system (BES) are required to comply with the North American Electric Reliability Corporation’s (NERC) reliability standards. All generators with greater than 20 MW at the BES connection must register as a Generator Owner (GO) and either register or assign a Generator Operator (GOP). On wind-power facilities the GO and GOP are typically the same entity.
Users, owners, and operators of the bulk electric system (BES) are required to comply with the North American Electric Reliability Corporation’s (NERC) reliability standards. All generators with greater than 20 MW at the BES connection must register as a Generator Owner (GO) and either register or assign a Generator Operator (GOP). On wind-power facilities the GO and GOP are typically the same entity.
Entities registered as a NERC GOP are responsible for complying with 39 NERC non-cyber security requirements regardless of who is performing the work. Requirements are grouped into standards, and then categories. The categories include Critical Infrastructure Protection (CIP), Communications (COM), Emergency Preparedness and Operations (EOP), Interconnection Reliability Operations and Coordination (IRO), Protection and Control (PRC), Transmission Operations (TOP), and Voltage and Reactive (VAR).
The GOP can face penalties when it’s non-compliant with NERC requirements. While most owners are aware of the need for such compliance, in our experience, there is less clarity on what this really entails. This article will address a few of the NERC requirements that have been identified as opportunities to improve compliance at wind-power facilities. These opportunities deal with TOP-001, Transmission Operations; CIP-001, Sabotage Reporting; CIP-002, Critical Cyber Asset Identification; and COM-002, Communications. We’ll summarize a few requirements and explain how they affect the wind industry.
Emergency operations
Requirement 1 of Standard TOP-001 reads: “Each Balancing Authority, Generator Operator, Distribution Provider, and Load-Serving Entity shall comply with each Reliability Directive issued and identified as such by its Transmission Operator(s), unless such action would violate safety, equipment, regulatory, or statutory requirements.”
Requirements 3 and 4 of EOP-001: Each Transmission Operator (TOP) shall have emergency plans that let it mitigate operating emergencies which includes the following two elements, which are particularly relevant for a wind power plant.
Element 10 reads: Maximizing generator output and availability — The operation of all generating sources to maximize output and availability (in the event of an emergency).
Element 11: Notifying independent power producers (IPP) — Notification of cogeneration and IPP to maximize output and availability.
What this means is that when the Transmission Operator calls to inform the wind-power GOP that an electrical emergency exists – one that presents the need to maximize output and availability – off-site and on-site operations and maintenance (O&M) personnel must be informed that all turbine outages and tuning must be suspended, and all available turbines brought online. In many wind power organizations, this may be an issue because communications is loosely coupled between the GOP, O&M personnel, and parties with remote control over the turbines, such as OEMs. When the GOP receives such a directive, all discretionary O&M, whether on site or via remote access, must be immediately curtailed. This can be particularly challenging when third-party service providers handle the O&M. Electrical emergencies that result in an outage, failed outage containment, or prolonged restoration will generally lead to an investigation by the Federal Energy Regulatory Commission and NERC. If a directive was given to maximize output and availability, and the maintenance staff curtailed turbine output during the emergency, the registered GOP may be found non-compliant with this and other requirements.
For the registered GOP to comply with TOP-001 during a grid emergency, wind-power entities must also consider third-party operation facilities and personnel as part of the process because the actions or inactions of the third party can impact the registered GOP’s compliance.
Sabotage reporting
Requirements 1 to 3 of Standard CIP-001 reads: Each GOP shall have procedures for recognizing, communicating, and ensuring that operating personnel are aware of sabotage events on its facilities and multi-site sabotage affecting larger portions of the Interconnection, and shall provide its operating personnel with sabotage-response guidelines. This includes personnel to contact, for reporting disturbances due to sabotage events.
In many wind-power organizations, the definition of “operating personnel” is blurred when some of them are off site or part of a third-party organization. When turbines can be controlled locally, as well as remotely off site, the definition of “operating personnel” extends to the remote personnel. Therefore, train all operating personnel, regardless of location or organizational affiliation, to establish a common under-standing of how to identify and respond in a sabotage event.
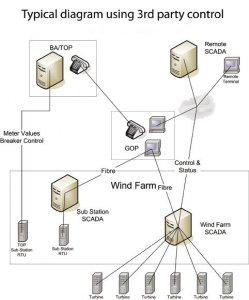
A typical SCADA configuration shown. If SCADA or other systems have control of turbines or breakers, they become part of the GOP’s cyber network regardless of location, owner, or operator.
Cyber security 
Requirement 1 of Standard CIP-002-4 (version 4, effective 4/1/2014): “Critical Asset Identification – The Responsible Entity shall develop a list of its identified Critical Assets determined through an annual application of the criteria contained in CIP-002-4 Attachment 1 – Critical Asset Criteria.”
As a general rule, individual wind-power facilities do not meet any of the criteria as a Critical Asset because they are not included in restoration plans and are not large enough to be critical to the BES. However Version 4 of the cyber security standards mandates that Supervisory Control and Data Acquisition (SCADA) systems meet a host of cyber security requirements if connected directly to a generation facility. The systems must also have control of 1,500 MW or more of any type of generation asset within an interconnection (Eastern, Western, or ERCOT), or control a resource defined as a Critical Asset.
This requirement presents challenges for the GOP at wind-power facilities because the GOP’s cyber network consists of the entire network of SCADA systems connected to a generating asset. The illustration Typical diagram using 3rd party control shows a typical configuration. If SCADA or other systems have control of turbines or breakers, they become part of the GOP’s cyber network regardless of location, owner, or operator, and it is the GOP’s responsibility to meet NERC requirements. Also, if another party owns and operates a remote SCADA system not registered with NERC, the system is not included in the GOP’s responsibilities. The third party need not register with NERC because the registered wind-power GOP is responsible for the cyber security of the control systems for the turbines or breakers. Therefore, the GOP must have audit-ready evidence that either:
- All control systems connected to projects do not meet any of the 17 criteria defined in CIP-002-4 Attachment 1 related to critical assets (one of which is control of 1,500 MW or more); or
- All Critical Cyber Assets associated with the turbine and breaker-control systems meet the remaining requirements in CIP-003-4 through CIP-009-4 as of April 1, 2014.
Communications
Requirement 1 of Standard COM-002: “Each Transmission Operator, Balancing Authority, and Generator Operator shall have communications (voice and data links) with appropriate Reliability Coordinators, Balancing Authorities, and Transmission Operators. Such communications shall be staffed and available for addressing a real-time emergency condition.”
When do real-time emergency conditions occur? Certainly not when GOPs want them to. Many wind-power GOPs do not have the resources to staff and equip a 24/7 operations center, hence a typical work-around has been to have the Balancing Authority or TOP install their own Remote Terminal Unit (RTU) for substation breaker control to curtail the wind farm when the GOP is not in a position to cut the wind power. This interface also lets the TOP and Balancing Authority read meter and meteorological data fulfilling data transfer requirements. This solution does not cover the emergency condition discussed above requiring maximum output and availability. If a GOP fails to receive and successfully communicate a reliability directive during an emergency, the registered GOP may be found non-compliant with multiple requirements related to following a directive.
Lastly, requirement 3 of VAR-002 reads: Each GOP shall notify its associated TOP within 30 minutes of any status or capability change on any generator reactive-power resource and the expected duration of the change in status or capability. That means if an automatic voltage regulator or capacitor bank were to change status and the GOP took more than 30 minutes to inform its TOP, the registered GOP may be found non-compliant.
Potential for penalties
The preceding examples highlight the importance of having clearly documented procedures and associated training to ensure that operating personnel understand and can comply with the details of NERC compliance requirements.
As a result of the Energy Policy Act of 2005, non-compliance with any of the potential 39 non-cyber requirements and 42 of the cyber security requirements that apply to the GOP can lead to substantial monetary fines. Enforcement of the requirements is rigorous. In 2012, there were 343 non-cyber and 301 cyber settlement negotiations with monetary fines, in some cases exceeding $1 million. These settlement negotiations do not include a larger number of violations that are handled under a Find, Fix, and Track process. It is also important that all NERC-registered entities have a robust compliance program to comply with the rules. As the Federal Energy Regulatory Commission has stated, “The presence of a robust internal compliance program is a mitigating factor that may result in a reduced penalty,” (FERC’s POLICY STATEMENT ON ENFORCEMENT (123 FERC | 61,156)).
Filed Under: Featured, Policy





I am with John, I have been trying to determine exactly what is required of Medium and Low Impact control centers for large solar plants.
What are the most important aspects of substation and collection system maintenance that most be performed by the wind farm owner.
Thank you very Much,
Chris Williams
Technical Diagnostic Services
817-475-1642 cell
What about solar facilities? What NERC standards apply to them?